Contrary to popular belief, businesses of any size can be at risk of hacking at any time. It is not uncommon for cybercriminals to steal sensitive data or cause disruption to your operations. You should be taking the necessary steps to ensure your company’s data is well protected at all times.
It is important to note that no matter how good your cyber security is, nothing is completely bulletproof. Cybercriminals know how to get past security solutions, and it could be the difference between your data being safe or stolen.
Cyber security threats are sometimes hard to notice and may even be well-masked. For example in an email perfectly designed to grab the attention of your employees.
You might have tried to reduce your risk of a cybersecurity breach already, but this does not mean the chances of you getting hacked are 0. In the following guide, Wave outlined how to react effectively should you find yourself in a dilemma¦
Recognise there is a problem, keep calm and take action
Cyber breaches are much more common than most businesses know. The longer a hack is ignored, the larger the chances are that more damage can be done. If someone within your company identifies issues, you must take action immediately. It is important to note that, no matter how severe, a cyber breach does not mean the end of your business.
Dealing with a cyber breach in an effective and timely manner ensures your reputation stays intact, and you don’t end up wasting your time. Although some damage may have already been done, the key is reducing the negative impact it can have on your business.
Sometimes hacking may be obvious but there are also more subtle indicators to look for which could suggest you have had a minor breach, or are in the process of being hacked.
A specialised IT expert would be able to identify more subtle hacker activity as they are familiar with the common indicators and know what they’re looking for. However, everyone should be vigilant and cautious if they come across something that seems out of the ordinary, such as:
- Reports from colleagues or contacts saying they’ve received some uncharacteristic emails from you containing links or attached files.
- Not being able to access certain files on your computer or while connected to the company network.
- Random notifications of login attempts to your accounts from times when you were not using them or locations that you havent been to.
- Changes to sensitive data in your systems, such as changes to financial systems and payment details.
- Frequent browser or system popups.
- The redirection of internet searches when you have typed in an address that you know is correct/have been to before.
If you suspect that you have been hacked, the best thing to do is take action quickly. Get the assistance of an IT specialist to help protect you from any further damage, as quickly as possible.
If your company has an internal or external IT support partner, inform them immediately. Reporting the situation as quickly as possible is the first step you should take.
If you do not have access to an IT specialist, you will need to find someone to assist you who has the skills necessary for the job. This is usually known as “cyber attach remediationâ€, and a quick google search should bring up specialists within your area.
No matter the size of your company, having an IT partner in place before a cyber breach happens will save you time, money and potentially your reputation.
Analyse the extent of the breach and remediate
Once you have recruited the help of an IT professional, they will begin scanning and identifying which elements of your network have been compromised. They may have to lock the system down to prevent a further breach. The best thing to do is to stay calm. This could be a small attack that has only compromised a single device, or the network.
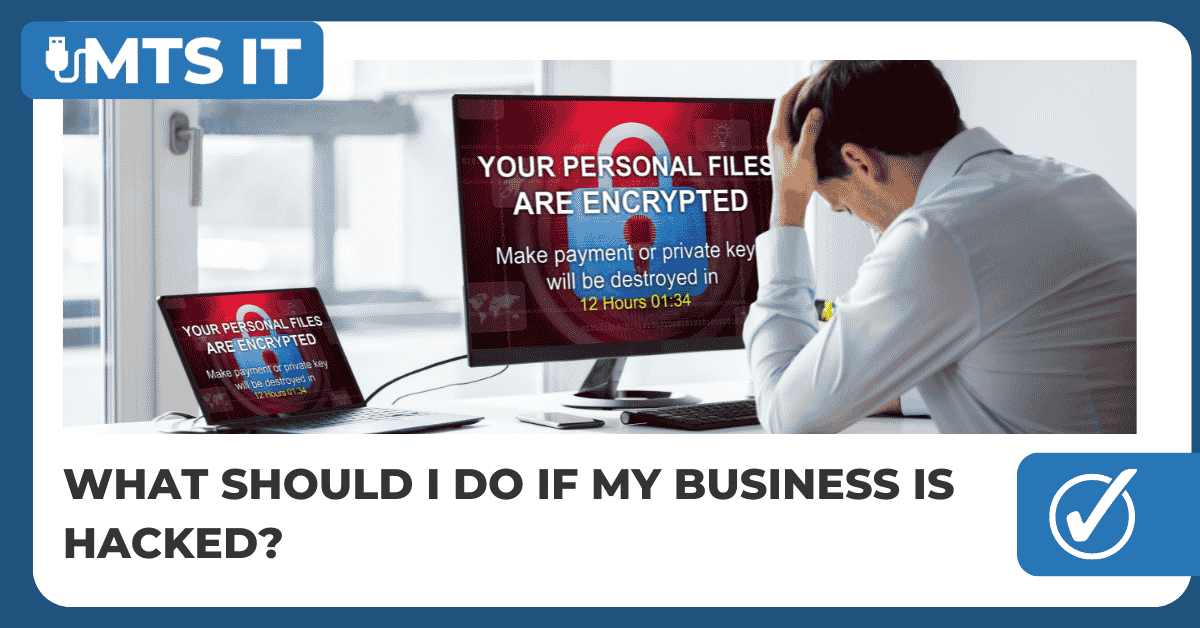
In recent years, one particular attack has become a lot more common, and is known as ‘ransomware’. This is when a piece of software encrypts files on a PC, laptop, server or any data storage device that it can access.
Ransomware is usually used to scramble data, preventing an end-user from accessing it. This means that you would be unable to access your compromised network. You would only be able to access it with a very complex key, which would allow you to unlock the files. In some circumstances, cybercriminals will request a ransom fee to hand over the key and give you access to the files.
No matter how you decide to take action, some next steps are necessary to consider as soon as you can, including…
Next steps you need to take
It is a legal requirement within the UK to report any data breaches within 72 hours of identifying an issue that involves the thanks to the new GDPR laws.
The ICO are the body that oversees GDPR, and they have a website that includes a large amount of helpful information on what to do. The website also contains a self-assessment form which is a free and easy way to understand if you need to report a possible breach.
The main question you will likely be asked is “what are you doing as a result of the breach?†Prompting a detailed plan from you outlining the ways you will be moving forward with increased data protection. You will likely need to provide a plan outlining these steps, which could include an altering of current procedures, heightened cyber security software and maybe some additional staff training.
It is important to ask your IT team or specialist if they can locate evidence of how the attack was initiated. This information will be key when moving forward with increased cyber security measures and could make you aware of a flaw in your security system, meaning you would be able to prevent it from happening again.
When you report a breach, it is not always guaranteed that you will be fined so long as you have taken the necessary steps to show that you have taken your cyber security seriously before the breach, and have a plan to improve it after. Providing as much detailed information on how you plan to ensure this doesn’t happen again in the future will ensure you are looked on more favourably in the future.
If you fail to report the breach, you may face much more serious consequences such as a very large fine or a percentage of your global turnover.
To talk more about how you can adequately prepare your cyber security system, talk to us at MTS IT on 0116 467 0155.